Legacy Active Directory Risk Assessment Guide for Enterprise IT Teams
Active Directory has been the backbone of enterprise identity for a long time. For many organizations, it has supported user authentication, access control, policy enforcement, and system administration for years without causing visible problems. That long-term reliability is one of the reasons so many businesses continue to rely on it heavily.
But that same familiarity often creates a false sense of security.
In many environments, Active Directory is still running, still supporting the business, and still doing what it was originally designed to do. Users can sign in. Applications can connect. Policies appear to function. Nothing seems obviously broken. From an operational point of view, it feels stable.
The issue is that stability and security are not the same thing.
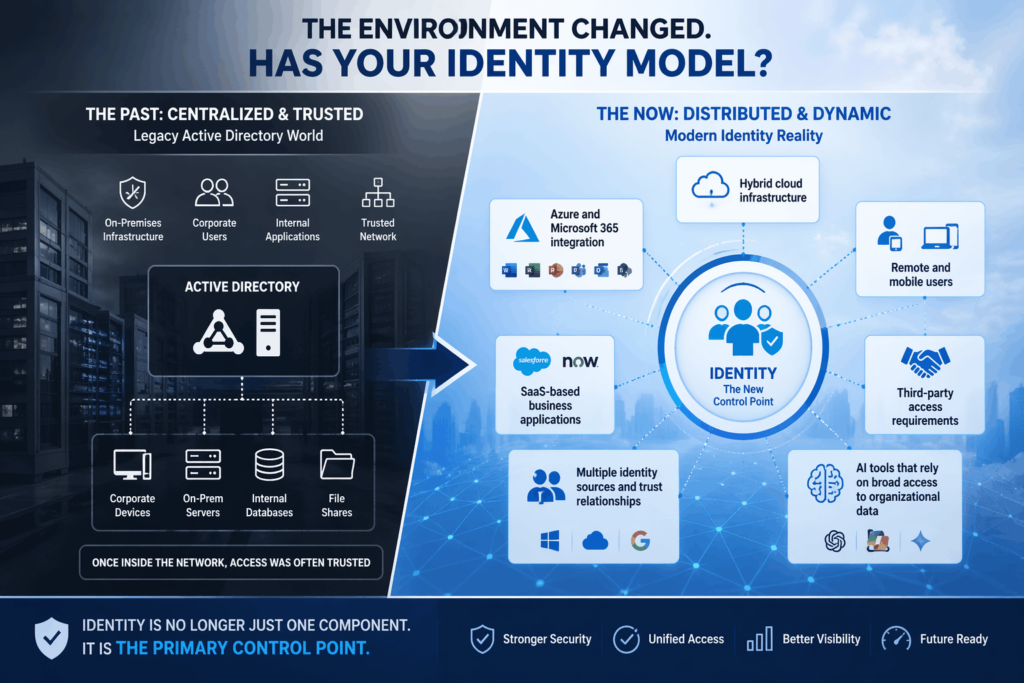
Modern enterprise environments have changed dramatically. Identity is no longer limited to internal office networks and company-managed desktops. Today, organizations operate across hybrid infrastructure, remote work models, SaaS applications, Azure services, third-party integrations, and increasingly, AI-enabled tools. In this kind of environment, identity has become the central control layer for access.
That means weaknesses inside Active Directory do not stay isolated. They can influence how users access cloud resources, how permissions are inherited, how trust relationships are maintained, and how attackers move once they gain a foothold.
This is why a legacy Active Directory review is no longer just a technical housekeeping exercise. It is a strategic security requirement.
This guide is designed to help enterprise IT leaders, infrastructure teams, and security stakeholders understand:
- Why legacy Active Directory environments can carry hidden risk even when they seem stable
- Where those risks commonly build up over time
- What an effective risk assessment should include
- How to prioritize improvements without creating unnecessary disruption
- Why identity reviews matter before larger initiatives such as Zero Trust, hybrid modernization, compliance preparation, or AI enablement
The goal of this guide is not to encourage a rip-and-replace approach. Most organizations do not need that. What they need is visibility, context, and a practical path forward.
Why Legacy Active Directory Deserves More Attention Now
When Active Directory was introduced, enterprise technology environments were far more centralized. Users worked primarily from corporate offices. Devices were usually company-managed and connected to internal networks. Applications ran mostly on-premises. The security model assumed that once a user or device was inside the network, it could often be trusted to some degree.
That assumption no longer holds.
Today’s enterprise environment is more distributed, more connected, and more dynamic. Organizations now deal with:
- Hybrid cloud infrastructure
- Azure and Microsoft 365 integration
- Remote and mobile users
- SaaS-based business applications
- Third-party access requirements
- Multiple identity sources and trust relationships
- AI tools that rely on broad access to organizational data
In that reality, identity is no longer just one security component. It is a primary control point.
When Active Directory remains tied to older assumptions while the environment around it modernizes, risk tends to grow quietly rather than suddenly.
The biggest problem is often “drift,” not obvious failure
Most enterprise AD environments do not become risky because of one dramatic mistake. The risk usually develops gradually.
A team adds a service account for a new application.
A trust relationship is created to support a business need.
A user gets added to a privileged group temporarily and never gets removed.
An old authentication method stays enabled because disabling it might affect something unknown.
A departed employee’s account is disabled but not fully cleaned up.
A policy is added in Azure, but it is not fully aligned with on-prem controls.
Each of these decisions may seem small and reasonable in isolation. Over several years, however, they create complexity, inconsistency, and blind spots.
That is what makes legacy identity risk so difficult to spot from day to day. The environment can feel operationally fine while becoming increasingly misaligned from a security and governance perspective.
The False Sense of Security in “Stable” Environments

One of the biggest reasons enterprise teams delay Active Directory reviews is simple: nothing urgent appears to be wrong.
That is understandable. IT teams are often measured by uptime, business continuity, service delivery, and issue resolution. If authentication is working and users are not complaining, AD is rarely the first thing that gets attention.
But this is exactly why risk can remain hidden.
A stable environment may still contain:
- Outdated authentication methods
- Stale permissions
- Inherited access that no longer makes sense
- Poorly governed administrative privileges
- Service accounts with weak oversight
- Security policy gaps between on-premises and cloud environments
None of these issues necessarily stops operations. In fact, many of them continue to work quietly in the background. But from a security standpoint, they increase exposure.
This is especially important in enterprise environments where identity is connected to critical systems, sensitive data, regulated workflows, and privileged administrative access. In those cases, even a single weak point can create a pathway for lateral movement or privilege escalation.
Just because a system is functioning normally does not mean it is aligned with modern security expectations.
That is the core message enterprise leaders need to understand when evaluating legacy identity infrastructure.
Identity Has Become the New Security Perimeter
Why identity matters more than ever
In the past, security strategies focused heavily on network boundaries. Firewalls, segmentation, and VPN controls played the main role in protecting internal systems.
Now, enterprise environments are far more identity-driven.
Access decisions depend on:
- Who the user is
- What device are they using
- Where they are signing in from
- What application or system are they trying to access
- What permissions do they already have
- Whether contextual controls like MFA or Conditional Access are being applied
This means identity systems are no longer just back-end administrative services. They are active participants in how access is granted or denied across the organization.
When Active Directory is part of that identity foundation, its configuration quality matters more than ever.
What this means for hybrid environments
In a hybrid setup, identity often spans multiple layers:
- On-prem Active Directory
- Azure AD / Microsoft Entra ID
- Microsoft 365
- SaaS applications
- VPN or remote access infrastructure
- Endpoint management tools
- Security monitoring platforms
If the on-prem identity layer contains inconsistencies or outdated controls, those issues can affect cloud security posture as well. That is why organizations moving toward Zero Trust or AI readiness often discover they need to review their identity foundation first.
Without that review, teams may build modern controls on top of a legacy structure that still contains hidden weaknesses.
How Real-World Identity Risk Usually Builds Up
Most enterprise breaches and security incidents tied to identity do not begin with someone “breaking” Active Directory directly. Instead, the issue is usually that attackers are able to use what already exists.
A common pattern looks like this:
- An attacker gains access through a compromised account, phishing success, or a weak endpoint.
- They begin exploring the environment using valid credentials or inherited permissions.
- They identify weak controls, unnecessary privileges, stale trusts, or overlooked accounts.
- They move laterally across systems or elevate access over time.
- Sensitive systems, data, or administrative controls become exposed.
This is why identity risk matters so much. In many cases, the environment is not “breached” through a dramatic technical failure. It is navigated through legitimate access pathways that were never cleaned up, reviewed, or constrained properly.
That is also why a risk assessment must look beyond whether AD is operational. The real question is whether the environment still reflects the organization’s current security, access, and governance needs.
Where Hidden Risks Commonly Exist in Legacy Active Directory
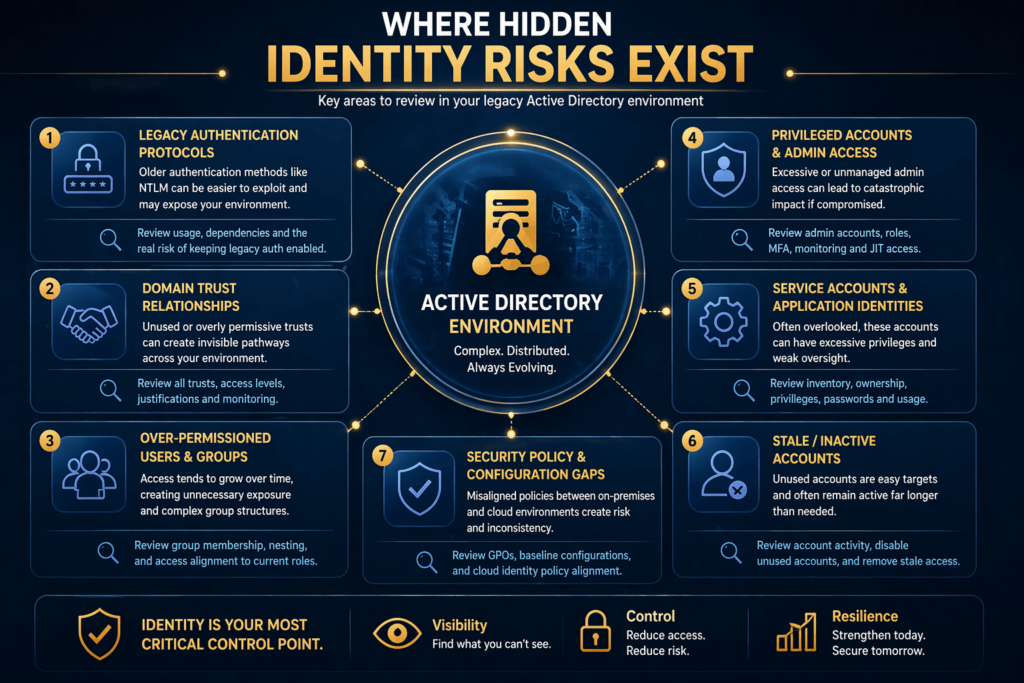
Below are some of the most important areas to review in a legacy AD environment. These are not random technical checks. They are places where risk tends to accumulate over time in large and growing organizations.
1. Legacy Authentication Protocols
Older authentication methods, especially NTLM, often remain enabled long after organizations begin modernizing their environment. This usually happens because teams are concerned about compatibility with older systems or applications.
The challenge is that older protocols can be harder to secure and more attractive to attackers. They may support weaker trust models, make credential abuse easier, or create opportunities for replay and lateral movement.
Why this matters:
- Legacy protocols often remain because “nothing has broken yet”
- They may be used by outdated applications, service dependencies, or unmanaged systems
- Their presence often signals that identity modernization is incomplete
What to review:
- Whether NTLM is still in active use
- Which systems or applications depend on it
- Whether more secure authentication methods are available
- Whether the business understands the real cost of keeping legacy auth enabled
This is not just a technical decision. It is a risk tradeoff. Organizations need to know where older authentication remains and whether that exposure is still justified.
2. Domain Trusts That No One Revisited
Trust relationships are often added for practical reasons. They help support acquisitions, business unit integration, shared resources, or temporary collaboration between domains.
The problem is that many trusts outlast their original purpose.
Over time, organizations may forget:
- Why the trust was created
- Whether it is still needed
- Whether the level of access it allows is still appropriate
- Whether the connected environment is governed by the same standard
An unnecessary or poorly governed trust relationship can create invisible access pathways across the environment. That becomes a serious issue if one side of the relationship is weaker than the other.
What to review:
- Inventory of all domain and forest trusts
- Business justification for each trust
- Level and direction of access allowed
- Whether controls and monitoring around the trust still make sense
In enterprise environments, trust relationships should not exist on historical assumption alone. They should be understood, documented, and periodically validated.
3. Over-Permissioned Users and Groups
Permission sprawl is one of the most common issues in long-running identity environments.
As employees change roles, teams grow, contractors come and go, and projects evolve, access tends to expand faster than it is reduced. It is common to find users with more access than they currently need, especially if permissions were layered over time instead of reviewed holistically.
This problem gets worse with groups.
Nested group structures, inherited permissions, and poorly documented admin access can make it very difficult to understand who truly has access to what.
Why this matters:
- Excess access increases the impact of account compromise
- It becomes harder to enforce least privilege
- Security reviews become more complex and time-consuming
- Teams may not realize how much access certain users or groups actually have
What to review:
- Membership in privileged groups
- Group nesting complexity
- Access assignments that no longer match current roles
- Whether least privilege principles are being applied consistently
This is one of the clearest examples of how operational convenience can gradually become security exposure.
4. Privileged Accounts and Admin Access
Administrative accounts deserve special attention because they can do the most damage if misused or compromised.
In many enterprise environments, privileged access has grown organically. Domain admins, local admins, delegated admins, break-glass accounts, and service administrators may all exist, but not always under a single governance model.
Important questions include:
- How many privileged accounts exist?
- Are they tied to named owners?
- Are they used only when needed or for daily work as well?
- Is access logged, reviewed, and constrained?
- Is privileged access separated from standard user activity?
A mature environment treats privileged access as a high-risk area that requires tighter control, not just stronger passwords.
What to review:
- Number and purpose of administrative accounts
- Whether privileged roles are still necessary
- Whether MFA, conditional access, and monitoring are in place
- Whether just-in-time or time-bound access models can reduce exposure
If a privileged account is compromised in a poorly governed environment, the impact is significantly higher than a normal user compromise
5. Service Accounts and Application Identities
Service accounts are often essential to business operations. They help applications run, connect systems, automate tasks, and support integrations.
But they are also one of the most neglected areas of identity governance.
Why? Service accounts usually do not belong to a single human owner in the same way a user account does. They may outlast the project they supported. Password rotation may be inconsistent. Monitoring is often weaker. In some cases, teams hesitate to touch them because they are afraid of breaking a critical system.
This creates several risks:
- Weak or unchanged credentials
- Excess permissions
- No clear ownership
- Limited visibility into usage
- Accounts that remain active long after they should have been retired
What to review:
- Inventory of service accounts
- Business ownership for each account
- Privileges assigned
- Password management approach
- Whether usage is still active and justified
A healthy identity environment treats service accounts as governed assets, not untouchable technical leftovers.
6. Inactive, Stale, and Orphaned Accounts
One of the simplest ways exposure grows in legacy AD is through stale accounts.
These may include:
- Former employee accounts not fully removed
- Disabled accounts still tied to access paths
- Test accounts left behind
- Vendor or contractor accounts no longer needed
- Accounts created for one-time projects
Even if these accounts are not actively used, their presence adds noise, complexity, and possible attack opportunities.
Why this matters:
- Old accounts may still have group memberships or permissions
- They can be forgotten during audits
- They weaken confidence in access governance
- Attackers often look for neglected accounts that are less likely to be monitored closely
What to review:
- Accounts inactive beyond a defined threshold
- Account lifecycle processes
- Whether deprovisioning includes full access cleanup
- Whether inactive accounts are still tied to privileged groups or service dependencies
Account cleanup may seem basic, but in large environments it is one of the most important foundations of identity hygiene.
6. Inactive, Stale, and Orphaned Accounts
One of the simplest ways exposure grows in legacy AD is through stale accounts.
These may include:
- Former employee accounts not fully removed
- Disabled accounts still tied to access paths
- Test accounts left behind
- Vendor or contractor accounts no longer needed
- Accounts created for one-time projects
Even if these accounts are not actively used, their presence adds noise, complexity, and possible attack opportunities.
Why this matters:
- Old accounts may still have group memberships or permissions
- They can be forgotten during audits
- They weaken confidence in access governance
- Attackers often look for neglected accounts that are less likely to be monitored closely
What to review:
- Accounts inactive beyond a defined threshold
- Account lifecycle processes
- Whether deprovisioning includes full access cleanup
- Whether inactive accounts are still tied to privileged groups or service dependencies
Account cleanup may seem basic, but in large environments it is one of the most important foundations of identity hygiene.
7. Conditional Access and Hybrid Policy Gaps
Many organizations have invested in modern cloud security controls such as Conditional Access, MFA, and risk-based access policies. That is a positive step.
The problem is that these controls are not always applied consistently across all users, devices, and systems.
In hybrid environments, it is common to see:
- Strong controls for cloud logins but weaker controls for legacy applications
- Exceptions added over time that were never re-evaluated
- Gaps between on-prem identity governance and cloud-based access enforcement
- Different standards for employees, contractors, and privileged users
This creates uneven protection. Teams may believe they have strong controls in place because policies exist, but if those policies do not cover all meaningful access paths, the security posture is weaker than it appears.
What to review:
- Which users and apps are covered by Conditional Access
- Where exceptions exist and why
- Whether legacy authentication bypasses modern controls
- Whether policy design reflects the current risk model
This is especially important for enterprises preparing for broader Microsoft 365, Azure, or AI adoption.
The 10 Most Important Checks in a Legacy AD Risk Assessment
Below is the heart of the guide: the checks that matter most in an enterprise-grade review. Each one should be evaluated in context, not as an isolated checkbox.
- Check for legacy authentication usage
Understand where older protocols are still enabled and what depends on them.
- Review trust relationships
Map every trust, confirm the business need, and assess the security implications.
- Audit privileged group membership
Identify who has elevated access and whether it is still justified.
- Evaluate service account governance
Confirm ownership, privileges, credential management, and active usage.
- Review inactive and stale accounts
Remove what is no longer needed and reduce unnecessary exposure.
- Assess permission sprawl
Look for excessive access, nested complexity, and role mismatch.
- Validate cloud and on-prem policy alignment
Ensure hybrid controls are not leaving gaps between environments.
- Review conditional access coverage
Confirm that policies cover meaningful identities, apps, and risk scenarios.
- Examine logging and visibility
Make sure authentication activity, privilege changes, and suspicious behavior are visible and reviewable.
- Establish a repeatable review process
Legacy identity risk is not solved once. It must be reviewed regularly as the environment changes.

What These Gaps Mean for the Business
Technical teams often understand why identity cleanup matters. Executive stakeholders, however, usually need the business context.
A weak legacy AD environment can lead to:
Higher security exposure
More unmanaged access paths mean more opportunity for compromise.
Slower incident response
When permissions, trusts, and ownership are unclear, investigations take longer.
Greater operational risk
Changes become harder to make confidently when the environment is poorly understood.
Compliance and audit friction
Access governance issues often surface during audits, assessments, or regulatory reviews.
Reduced readiness for strategic initiatives
Organizations cannot fully benefit from Zero Trust, AI, or cloud modernization if their identity foundation still carries unmanaged risk.
This is why legacy identity should not be seen as a narrow infrastructure issue. It affects resilience, governance, transformation readiness, and business confidence.
How to Improve Without Disruption
A common reason teams postpone AD reviews is fear of breaking something important. That concern is valid. Enterprise identity environments are deeply connected to core operations.
The answer is not aggressive change. It is controlled prioritization.
A practical modernization approach usually looks like this:
Start with visibility
Before changing anything, build a clear view of what exists.
Identify high-risk, low-disruption opportunities
Some issues can be reduced quickly with limited operational impact.
Separate urgent cleanup from long-term modernization
Not every issue needs to be solved immediately. Some need planning, not panic.
Create ownership
Each risky area should have a responsible stakeholder, not just a technical note.
Build review into governance
Identity risk assessment should become a repeatable discipline, not a one-time project.
This approach helps organizations improve safety while maintaining operational continuity.
When an Active Directory Review Becomes Especially Important
There are certain business and technical moments when a legacy AD review becomes much more urgent.
Before Zero Trust initiatives
Zero Trust depends on strong identity controls. Weak foundations make policy enforcement less effective.
Before major Azure or cloud expansion
If hybrid identity is central to the cloud model, legacy gaps need attention first.
Before AI or Copilot enablement
AI tools often rely on broad access to organizational information. Poor identity governance increases risk.
After a merger or acquisition
Directory integration often creates new trust relationships, stale accounts, overlapping permissions, and governance complexity.
During audit or compliance preparation
Access clarity and identity hygiene become much more important under scrutiny.
After a leadership or structural change in IT
New leadership often discovers that long-running identity environments have not been reviewed deeply in years.
These trigger moments matter because they expose how much the business now depends on identity being clean, controlled, and current.
Conclusion
Legacy Active Directory environments are rarely ignored because teams do not care. They are usually overlooked because they keep working.
That reliability, however, can hide the real problem.
In modern enterprise environments, identity has become too important to leave on historical assumption. A directory that still functions operationally may still contain outdated protocols, inherited privileges, unmanaged trusts, weak service account governance, and hybrid policy gaps that increase risk quietly over time.
The purpose of a legacy AD risk assessment is not to criticize the past. It is to create visibility into the present.
When organizations review identity with the right level of depth, they usually do not find one dramatic failure. They find multiple small issues that, together, deserve attention. That is what makes the review valuable. It replaces uncertainty with clarity and complexity with prioritization.
For enterprises moving toward Zero Trust, cloud maturity, stronger compliance, or AI readiness, this review is not optional for long. It is one of the smartest steps they can take to reduce hidden risk before it becomes visible the hard way.
Key Takeaways
- A stable Active Directory environment is not automatically a secure one.
- Legacy identity risk usually builds through drift, not obvious failure.
- Hybrid environments make AD weaknesses more relevant, not less.
- Common risk areas include legacy authentication, trust relationships, stale accounts, over-permissioned users, and service account sprawl.
- Identity reviews are especially important before Zero Trust, cloud expansion, M&A integration, compliance reviews, or AI enablement.
- The goal is not disruption. It is visibility, prioritization, and controlled improvement.
Frequently Asked Questions
Why should we review Active Directory if it has been working fine for years?
This is one of the most common and most important questions.
The reason is that “working fine” usually means the environment is operational, not necessarily secure or well-governed. Active Directory can continue supporting logins, policies, and access requests for years while still accumulating issues in the background.
Over time, permissions change, old systems remain connected, service accounts are added, temporary access becomes permanent, and trust relationships evolve. None of this may cause visible disruption. But together, these changes can create security exposure that only becomes obvious when an audit, incident, or modernization effort forces a closer look.
So the question is not whether AD is still functioning. The question is whether it still reflects the organization’s current access, security, and governance requirements.
Does reviewing legacy Active Directory mean we need to replace it?
No. In most cases, it does not.
A risk assessment is not the same as a replacement project. The purpose of the review is to understand what exists, where the biggest risks are, and what improvements would make the environment more secure and manageable.
For many organizations, the right next step is not replacing AD. It is improving governance around it, reducing outdated dependencies, tightening privileged access, cleaning up stale accounts, and aligning on-prem identity with modern cloud security controls.
In other words, the assessment is about making better decisions. Sometimes that leads to larger modernization efforts later, but often it begins with smaller, high-impact improvements.
What are the most common problems found in older AD environments?
The most common issues are usually not dramatic technical failures. They tend to be governance and hygiene problems that build over time.
Examples include:
- Legacy authentication protocols that were never fully retired
- Accounts with more access than users need
- Unused domain trusts that remain active
- Service accounts with weak ownership or poor password rotation
- Inactive accounts that were never fully removed
- Conditional access gaps between on-prem and cloud usage
- Complex group nesting that makes permissions hard to understand
What makes these issues serious is not just their individual presence. It is the way they interact. One overlooked service account might not seem critical, but combined with excessive permissions and weak monitoring, it can create a meaningful security gap.
How often should an enterprise review Active Directory risk?
There is no single schedule that fits every organization, but for most enterprises, identity should be reviewed regularly rather than only during crisis or change.
At a minimum, organizations should conduct structured reviews:
- Annually
- Before major cloud or Zero Trust initiatives
- After mergers, acquisitions, or organizational restructuring
- Before major audits or compliance reviews
- When leadership suspects privilege sprawl or governance drift
More mature organizations may review certain areas, such as privileged access or stale accounts, much more frequently.
The important thing is not just the frequency. It is making identity review part of governance rather than treating it as a one-off cleanup exercise.
Why does legacy AD matter so much in hybrid cloud environments?
Because hybrid environments increase the importance of identity consistency.
In a hybrid model, Active Directory often continues to influence access across on-prem systems, Azure, Microsoft 365, and connected applications. If that identity foundation contains outdated controls or poorly governed access, the risk can extend beyond the data center into the broader cloud environment.
This matters because modern access decisions are often interconnected. A weak identity control on one side of the environment can undermine stronger controls on the other.
That is why enterprises investing in Azure, Conditional Access, Entra ID, and cloud productivity tools often need to reassess their legacy identity foundation first. Otherwise, they risk layering modern controls on top of older structures that still contain unmanaged weaknesses.
What is the business value of doing this kind of review?
The value goes beyond security.
A strong identity review helps organizations:
- Reduce hidden access risk
- Improve governance and audit readiness
- Strengthen the foundation for Zero Trust and cloud modernization
- Make access control more understandable and defensible
- Lower the impact of account compromise
- Increase confidence in transformation initiatives
In practical terms, it gives the business better visibility into how access is really being managed and where silent risk may be sitting.
That clarity is valuable for IT, security, compliance, and leadership teams alike.
Is this only relevant for highly regulated industries?
No. Regulated industries may feel the urgency more strongly because of audit pressure, but the underlying identity risks affect a much wider range of enterprise organizations.
Any business with:
- Hybrid infrastructure
- Sensitive internal data
- Privileged IT operations
- Remote users
- Cloud-connected systems
- Growth through acquisitions
- Expanding AI or automation initiatives
can benefit from reviewing legacy Active Directory risk.
The need is not limited to compliance-heavy sectors. It applies broadly to organizations whose operations rely on identity being trustworthy, current, and properly governed.
Can we improve AD security without causing downtime or user disruption?
Yes, in many cases you can.
That is one of the main reasons a structured assessment matters. It helps teams separate low-risk cleanup opportunities from more sensitive or complex changes. Not every improvement requires major disruption.
For example, organizations can often begin by:
- Inventorying trusts and privileged accounts
- Reviewing stale accounts
- Improving service account ownership
- Identifying legacy authentication dependencies
- Tightening monitoring and visibility
These actions can create momentum and reduce exposure without immediately changing core production behavior.
The key is to approach improvements in phases, with clear prioritization and testing where needed.
How does this connect to Zero Trust?
Zero Trust depends on strong identity control.
If an organization wants to enforce “never trust, always verify,” then it needs to know:
- Who has access
- How authentication works
- Where privileges are concentrated
- Whether policy coverage is consistent
- Whether legacy access paths can bypass modern controls
A poorly governed Active Directory environment makes Zero Trust harder to implement effectively. Policies may exist, but their impact is reduced if the underlying identity environment is still carrying unmanaged risk.
That is why many Zero Trust journeys eventually come back to identity hygiene and access governance. It is difficult to build a strong verification model on top of unclear privilege structures and outdated authentication dependencies.
